配置NAT表及路由选择
电脑发包源地址:192.168.1.10:xxx] 转换为 [路由 A:192.168.2.5:xxx] 转换为 [路由 B:192.168.3.6:xxx] 转换为 [路由 C:172.16.2.5:xxx] 转换为 [光猫:110.x.x.x:xxx(公网地址)]从光猫这个互联网接入路由器上源地址变成公网地址后,后面经过的运营商骨干路由器、城域网路由器,一路到外网服务器只做普通路由转发,不做
目录
路由器的 NAT 地址转换
局域网内多层路由器串联,每经过一次家用路由器(非桥接),NAT 地址就会转换一次:每一层路由器都会做一次私网→上一级网段的地址(网关地址)转换:IP、端口都会变
一、先搞懂:家用路由器默认都开 NAT
家用路由的 WAN 口接上级网络,LAN 口接下一级设备 / 下级路由:
LAN 侧:私网 IP(192.168.x.x / 10.x.x.x / 172.16–31)
WAN 侧:拿到上级分配的 IP
只要是路由模式、不是桥接,就一定做 NAT 地址转换
二、举个实例:3 层路由器串联
设备 → 路由 A → 路由 B → 路由 C → 光猫 → 外网
1. 设备内网 IP
192.168.1.10
2. 经过路由 A(第一次 NAT)
路由 A 把 192.168.1.10 转换成 路由 A 的 WAN 口 IP:比如变成 192.168.2.5:随机端口
3. 经过路由 B(第二次 NAT)
路由 B 再把 192.168.2.5 转换成 路由 B 的 WAN 口 IP:比如变成 192.168.3.6:新随机端口
4. 经过路由 C(第三次 NAT)
再转一次,换成路由 C 的 WAN 口 IP + 新端口
5. 最后出外网
再经过光猫 NAT,变成公网 IP
小结:每过一台局域网普通路由器,就多一次 NAT:换一次 IP、换一次端口
三、两种特殊情况不重复转换
下级路由器改成「桥接模式 / AP 模式」只做转发(当成交换机使用),不做 NAT、不分配 DHCP,地址不转换,相当于一根网线延长
路由器之间用静态路由、纯三层路由(关闭 NAT)全程路由转发,无 NAT,IP 从头到尾不变,企业网络常用
四、多层 NAT 带来的问题
端口映射只能在最外层路由生效,内层做了也没用
P2P、游戏联机、远程访问很难打通
网络延迟略增加,多层 NAT 损耗
排查抓包更复杂,每一层看到的源 IP 都不一样
五、简单记忆
家用路由默认串联 = 每层都 NAT,地址层层转换
改成 AP / 桥接 = 不做 NAT,地址不变
六、总结
1. 正常不做 NAT 的路由器只转发、不改 IP:源 IP 从头到尾永远不变,目的 IP 从头到尾永远不变,只有 MAC 地址每过一跳路由器就变一次,IP 负责端到端、MAC 负责下一跳
2. 全过程例子
内网电脑 → 路由 A(NAT) → 路由 B(NAT) → 路由 C(NAT) → 光猫(NAT) → 运营商网络 → 外网服务器
[电脑发包源地址:192.168.1.10:xxx] 转换为 [路由 A:192.168.2.5:xxx] 转换为 [路由 B:192.168.3.6:xxx] 转换为 [路由 C:172.16.2.5:xxx] 转换为 [光猫:110.x.x.x:xxx(公网地址)]
从光猫这个互联网接入路由器上源地址变成公网地址后,后面经过的运营商骨干路由器、城域网路由器,一路到外网服务器只做普通路由转发,不做 NAT,所以不会再改你的源 IP,即源 IP 永远固定是这个公网 IP
NAT配置及路由选择的实例说明
一、未配置NAT表
1、网络配置
#虚拟机A(192.168.2.111)
~# ifconfig ens33
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.220.108 netmask 255.255.255.0 broadcast 192.168.220.255
inet6 fe80::20c:29ff:fed1:462e prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:d1:46:2e txqueuelen 1000 (Ethernet)
RX packets 3388 bytes 391690 (382.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 865 bytes 129270 (126.2 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
~# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.220.2 0.0.0.0 UG 0 0 0 ens33
192.168.220.0 0.0.0.0 255.255.255.0 U 0 0 0 ens33
~# curl www.baidu.com &>/dev/null && echo $?
0
VMware点击虚拟机-设置-硬件-添加网络适配器[NAT模式]-确定(虚拟机AB分别添加网卡ens37)
~# ps -ef|grep dhclient|grep -v grep &>/dev/null && bash -c "systemctl stop NetworkManager;systemctl disable NetworkManager" #停止dhclient自启动,脱离NetworkManager服务
~# iptables -F
~# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:d1:46:2e brd ff:ff:ff:ff:ff:ff
inet 192.168.220.108/24 brd 192.168.220.255 scope global ens33
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:fed1:462e/64 scope link
valid_lft forever preferred_lft forever
3: ens37: <BROADCAST,MULTICAST> mtu 1500 qdisc noop state DOWN group default qlen 1000
link/ether 00:0c:29:d1:46:38 brd ff:ff:ff:ff:ff:ff
~# ifconfig ens37 192.168.2.111 netmask 255.255.255.0 #分配ip地址.添加路由(route add -net 192.168.2.0 netmask 255.255.255.0 dev ens37)
~# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.220.2 0.0.0.0 UG 0 0 0 ens33
192.168.2.0 0.0.0.0 255.255.255.0 U 0 0 0 ens37
192.168.220.0 0.0.0.0 255.255.255.0 U 0 0 0 ens33
#虚拟机B(192.168.2.110)
VMware点击虚拟机-设置-硬件-添加网络适配器[NAT模式]-确定(虚拟机AB分别添加网卡ens37)
~# ps -ef|grep dhclient|grep -v grep &>/dev/null && bash -c "systemctl stop NetworkManager;systemctl disable NetworkManager" #停止dhclient自启动,脱离NetworkManager服务
~# iptables -F
~# ifconfig ens33 down
~# ifconfig ens37 192.168.2.110 netmask 255.255.255.0 #分配ip地址.添加路由(route add -net 192.168.2.0 netmask 255.255.255.0 dev ens37)
~# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
192.168.2.0 0.0.0.0 255.255.255.0 U 0 0 0 ens37
~# route add default gw 192.168.2.111 dev ens37 #添加192.168.2.111为默认网关
~# route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.2.111 0.0.0.0 UG 0 0 0 ens37
192.168.2.0 0.0.0.0 255.255.255.0 U 0 0 0 ens37
2、虚拟机A(192.168.2.111)开启转发功能并监测数据包
~# echo 1 >/proc/sys/net/ipv4/ip_forward
3、虚拟机B(192.168.2.110)和虚拟机A(192.168.2.111)执行
~# conntrack -F
~# tcpdump tcp and port 80 -i any -nv &>>/tmp/result.txt &
4.1、虚拟机B(192.168.2.110)执行
~# curl www.baidu.com &>/dev/null && echo $?
0
~# conntrack -p tcp -L
tcp 6 118 TIME_WAIT src=192.168.2.110 dst=183.2.172.177 sport=58260 dport=80 src=183.2.172.177 dst=192.168.2.110 sport=80 dport=58260 [ASSURED] mark=0 use=1
conntrack v1.4.4 (conntrack-tools): 1 flow entries have been shown.
~# cat /tmp/result.txt
tcpdump: listening on any, link-type LINUX_SLL (Linux cooked), capture size 262144 bytes
15:44:50.911154 IP (tos 0x0, ttl 64, id 16249, offset 0, flags [DF], proto TCP (6), length 60)
192.168.2.110.60860 > 183.2.172.177.http: Flags [S], cksum 0x26f9 (incorrect -> 0x1a8c), seq 1691881617, win 29200, options [mss 1460,sackOK,TS val 20656104 ecr 0,nop,wscale 7], length 0
15:44:50.945208 IP (tos 0x0, ttl 127, id 630, offset 0, flags [none], proto TCP (6), length 44)
183.2.172.177.http > 192.168.2.110.60860: Flags [S.], cksum 0x7b94 (correct), seq 1278102305, ack 1691881618, win 64240, options [mss 1460], length 0
15:44:50.945258 IP (tos 0x0, ttl 64, id 16250, offset 0, flags [DF], proto TCP (6), length 40)
192.168.2.110.60860 > 183.2.172.177.http: Flags [.], cksum 0x26e5 (incorrect -> 0x1c32), ack 1, win 29200, length 0
15:44:50.945405 IP (tos 0x0, ttl 64, id 16251, offset 0, flags [DF], proto TCP (6), length 117)
192.168.2.110.60860 > 183.2.172.177.http: Flags [P.], cksum 0x2732 (incorrect -> 0xd8f7), seq 1:78, ack 1, win 29200, length 77: HTTP, length: 77
GET / HTTP/1.1
User-Agent: curl/7.29.0
Host: www.baidu.com
Accept: */*
15:44:50.946345 IP (tos 0x0, ttl 127, id 631, offset 0, flags [none], proto TCP (6), length 40)
183.2.172.177.http > 192.168.2.110.60860: Flags [.], cksum 0x9304 (correct), ack 78, win 64240, length 0
15:44:50.975036 IP (tos 0x0, ttl 127, id 632, offset 0, flags [none], proto TCP (6), length 829)
183.2.172.177.http > 192.168.2.110.60860: Flags [P.], cksum 0xcfed (correct), seq 1:790, ack 78, win 64240, length 789: HTTP, length: 789
HTTP/1.1 200 OK
Cache-Control: private, no-cache, no-store, proxy-revalidate, no-transform
Content-Length: 2381
Content-Type: text/html
Pragma: no-cache
Server: bfe
Set-Cookie: BDORZ=27315; max-age=86400; domain=.baidu.com; path=/
Date: Wed, 29 Apr 2026 07:44:50 GMT
4.2、虚拟机A(192.168.2.111)执行
~# conntrack -p tcp -L #通过虚拟机A(192.168.2.111)转发的(src=192.168.2.110)数据包本机不会接收,所以状态是UNREPLIED
tcp 6 114 SYN_SENT src=192.168.2.110 dst=183.2.172.177 sport=58260 dport=80 [UNREPLIED] src=183.2.172.177 dst=192.168.2.110 sport=80 dport=58260 mark=0 use=1
conntrack v1.4.4 (conntrack-tools): 1 flow entries have been shown.
~# cat /tmp/result.txt #未捕获到相关数据包,虽然启用了NAT转发功能但是未配置NAT表(路由器的转发自动做地址映射,linux的转发功能需要配置NAT表手动做地址映射!!!!!!)
tcpdump: listening on any, link-type LINUX_SLL (Linux cooked), capture size 262144 bytes
5、分析总结
虚拟机B(192.168.2.110)执行curl www.baidu.com数据包:192.168.2.110:58260→183.2.172.177:80,虚拟机B(192.168.2.110)去往183.2.172.177地址的数据包交给网关192.168.2.111进行转发.这条数据包经过主机192.168.2.111到虚拟网络VMnet8(192.168.220.2)映射为无线网卡地址:端口后继续传输!
此环境下在没有配置NAT表(iptables -t nat -A POSTROUTING -s 192.168.2.110/32 -j SNAT --to 192.168.220.108)的情况下,从结果来看虚拟机B(192.168.2.110)访问成功,但是未明白192.168.2.110这个地址在虚拟网络VMnet8(192.168.220.2)这个路由器上是如何返回到主机虚拟机B(192.168.2.110)的[因为虚拟网络VMnet8(192.168.220.2)没有192.168.2.0/24网段的路由].因此在网关的虚拟机A(192.168.2.111)上配置NAT表(iptables -t nat -A POSTROUTING -s 192.168.2.110/32 -j SNAT --to 192.168.220.108)完成源地址192.168.2.110:xxx转换为192.168.220.108:xxx
6、说明
虚拟网络VMnet8和宿主机无线网卡配置及报文见下方图1图2
二、配置NAT表
1、虚拟机A(192.168.2.111)执行
~# iptables -t nat -A POSTROUTING -s 192.168.2.110/32 -j SNAT --to 192.168.220.108
2、虚拟机B(192.168.2.110)和虚拟机A(192.168.2.111)执行
~# ps -ef|grep tcpdump|grep -v grep|awk '{print $2}'|xargs -n 1 kill -9
~# rm -rf /tmp/result.txt
~# tcpdump tcp and port 80 -i any -nv &>/tmp/result.txt &
3、虚拟机B(192.168.2.110)执行
~# curl www.baidu.com &>/dev/null && echo $?
0
~# conntrack -p tcp -L
tcp 6 51 TIME_WAIT src=192.168.2.110 dst=183.2.172.177 sport=60886 dport=80 src=183.2.172.177 dst=192.168.2.110 sport=80 dport=60886 [ASSURED] mark=0 use=1
conntrack v1.4.4 (conntrack-tools): 1 flow entries have been shown.
~# cat /tmp/result.txt
tcpdump: listening on any, link-type LINUX_SLL (Linux cooked), capture size 262144 bytes
17:29:35.286545 IP (tos 0x0, ttl 64, id 45035, offset 0, flags [DF], proto TCP (6), length 60)
192.168.2.110.60886 > 183.2.172.177.http: Flags [S], cksum 0x26f9 (incorrect -> 0x73b1), seq 2586247354, win 29200, options [mss 1460,sackOK,TS val 52080465 ecr 0,nop,wscale 7], length 0
17:29:35.318411 IP (tos 0x0, ttl 127, id 1374, offset 0, flags [none], proto TCP (6), length 44)
183.2.172.177.http > 192.168.2.110.60886: Flags [S.], cksum 0x29ee (correct), seq 1293973059, ack 2586247355, win 64240, options [mss 1460], length 0
17:29:35.318480 IP (tos 0x0, ttl 64, id 45036, offset 0, flags [DF], proto TCP (6), length 40)
192.168.2.110.60886 > 183.2.172.177.http: Flags [.], cksum 0x26e5 (incorrect -> 0xca8b), ack 1, win 29200, length 0
17:29:35.318683 IP (tos 0x0, ttl 64, id 45037, offset 0, flags [DF], proto TCP (6), length 117)
192.168.2.110.60886 > 183.2.172.177.http: Flags [P.], cksum 0x2732 (incorrect -> 0x8751), seq 1:78, ack 1, win 29200, length 77: HTTP, length: 77
GET / HTTP/1.1
User-Agent: curl/7.29.0
Host: www.baidu.com
Accept: */*
17:29:35.319890 IP (tos 0x0, ttl 127, id 1375, offset 0, flags [none], proto TCP (6), length 40)
183.2.172.177.http > 192.168.2.110.60886: Flags [.], cksum 0x415e (correct), ack 78, win 64240, length 0
17:29:35.350975 IP (tos 0x0, ttl 127, id 1376, offset 0, flags [none], proto TCP (6), length 829)
183.2.172.177.http > 192.168.2.110.60886: Flags [P.], cksum 0x7440 (correct), seq 1:790, ack 78, win 64240, length 789: HTTP, length: 789
HTTP/1.1 200 OK
Cache-Control: private, no-cache, no-store, proxy-revalidate, no-transform
Content-Length: 2381
Content-Type: text/html
Pragma: no-cache
Server: bfe
Set-Cookie: BDORZ=27315; max-age=86400; domain=.baidu.com; path=/
Date: Thu, 30 Apr 2026 09:29:35 GMT
<!DOCTYPE html>
4、虚拟机A(192.168.2.111)执行
~# conntrack -p tcp -L
tcp 6 51 TIME_WAIT src=192.168.2.110 dst=183.2.172.177 sport=60886 dport=80 src=183.2.172.177 dst=192.168.220.108 sport=80 dport=60886 [ASSURED] mark=0 use=1
conntrack v1.4.4 (conntrack-tools): 1 flow entries have been shown.
~# cat /tmp/result.txt
tcpdump: listening on any, link-type LINUX_SLL (Linux cooked), capture size 262144 bytes
17:29:35.288249 IP (tos 0x0, ttl 64, id 45035, offset 0, flags [DF], proto TCP (6), length 60)
192.168.2.110.60886 > 183.2.172.177.http: Flags [S], cksum 0x73b1 (correct), seq 2586247354, win 29200, options [mss 1460,sackOK,TS val 52080465 ecr 0,nop,wscale 7], length 0
17:29:35.288286 IP (tos 0x0, ttl 63, id 45035, offset 0, flags [DF], proto TCP (6), length 60)
192.168.220.108.60886 > 183.2.172.177.http: Flags [S], cksum 0x99b2 (correct), seq 2586247354, win 29200, options [mss 1460,sackOK,TS val 52080465 ecr 0,nop,wscale 7], length 0
17:29:35.319703 IP (tos 0x0, ttl 128, id 1374, offset 0, flags [none], proto TCP (6), length 44)
183.2.172.177.http > 192.168.220.108.60886: Flags [S.], cksum 0x4fef (correct), seq 1293973059, ack 2586247355, win 64240, options [mss 1460], length 0
17:29:35.319734 IP (tos 0x0, ttl 127, id 1374, offset 0, flags [none], proto TCP (6), length 44)
183.2.172.177.http > 192.168.2.110.60886: Flags [S.], cksum 0x29ee (correct), seq 1293973059, ack 2586247355, win 64240, options [mss 1460], length 0
17:29:35.320061 IP (tos 0x0, ttl 64, id 45036, offset 0, flags [DF], proto TCP (6), length 40)
192.168.2.110.60886 > 183.2.172.177.http: Flags [.], cksum 0xca8b (correct), ack 1, win 29200, length 0
17:29:35.320082 IP (tos 0x0, ttl 63, id 45036, offset 0, flags [DF], proto TCP (6), length 40)
192.168.220.108.60886 > 183.2.172.177.http: Flags [.], cksum 0xf08c (correct), ack 1, win 29200, length 0
17:29:35.320244 IP (tos 0x0, ttl 64, id 45037, offset 0, flags [DF], proto TCP (6), length 117)
192.168.2.110.60886 > 183.2.172.177.http: Flags [P.], cksum 0x8751 (correct), seq 1:78, ack 1, win 29200, length 77: HTTP, length: 77
GET / HTTP/1.1
User-Agent: curl/7.29.0
Host: www.baidu.com
Accept: */*
17:29:35.320250 IP (tos 0x0, ttl 63, id 45037, offset 0, flags [DF], proto TCP (6), length 117)
192.168.220.108.60886 > 183.2.172.177.http: Flags [P.], cksum 0xad52 (correct), seq 1:78, ack 1, win 29200, length 77: HTTP, length: 77
GET / HTTP/1.1
User-Agent: curl/7.29.0
Host: www.baidu.com
Accept: */*
17:29:35.321268 IP (tos 0x0, ttl 128, id 1375, offset 0, flags [none], proto TCP (6), length 40)
183.2.172.177.http > 192.168.220.108.60886: Flags [.], cksum 0x675f (correct), ack 78, win 64240, length 0
17:29:35.321274 IP (tos 0x0, ttl 127, id 1375, offset 0, flags [none], proto TCP (6), length 40)
183.2.172.177.http > 192.168.2.110.60886: Flags [.], cksum 0x415e (correct), ack 78, win 64240, length 0
17:29:35.352328 IP (tos 0x0, ttl 128, id 1376, offset 0, flags [none], proto TCP (6), length 829)
183.2.172.177.http > 192.168.220.108.60886: Flags [P.], cksum 0x9a41 (correct), seq 1:790, ack 78, win 64240, length 789: HTTP, length: 789
HTTP/1.1 200 OK
Cache-Control: private, no-cache, no-store, proxy-revalidate, no-transform
Content-Length: 2381
Content-Type: text/html
Pragma: no-cache
Server: bfe
Set-Cookie: BDORZ=27315; max-age=86400; domain=.baidu.com; path=/
Date: Thu, 30 Apr 2026 09:29:35 GMT
<!DOCTYPE html>
17:29:35.352358 IP (tos 0x0, ttl 127, id 1376, offset 0, flags [none], proto TCP (6), length 829)
183.2.172.177.http > 192.168.2.110.60886: Flags [P.], cksum 0x7440 (correct), seq 1:790, ack 78, win 64240, length 789: HTTP, length: 789
HTTP/1.1 200 OK
Cache-Control: private, no-cache, no-store, proxy-revalidate, no-transform
Content-Length: 2381
Content-Type: text/html
Pragma: no-cache
Server: bfe
Set-Cookie: BDORZ=27315; max-age=86400; domain=.baidu.com; path=/
Date: Thu, 30 Apr 2026 09:29:35 GMT
<!DOCTYPE html>
5、说明
虚拟网络VMnet8和宿主机无线网卡配置及报文见下方图3图4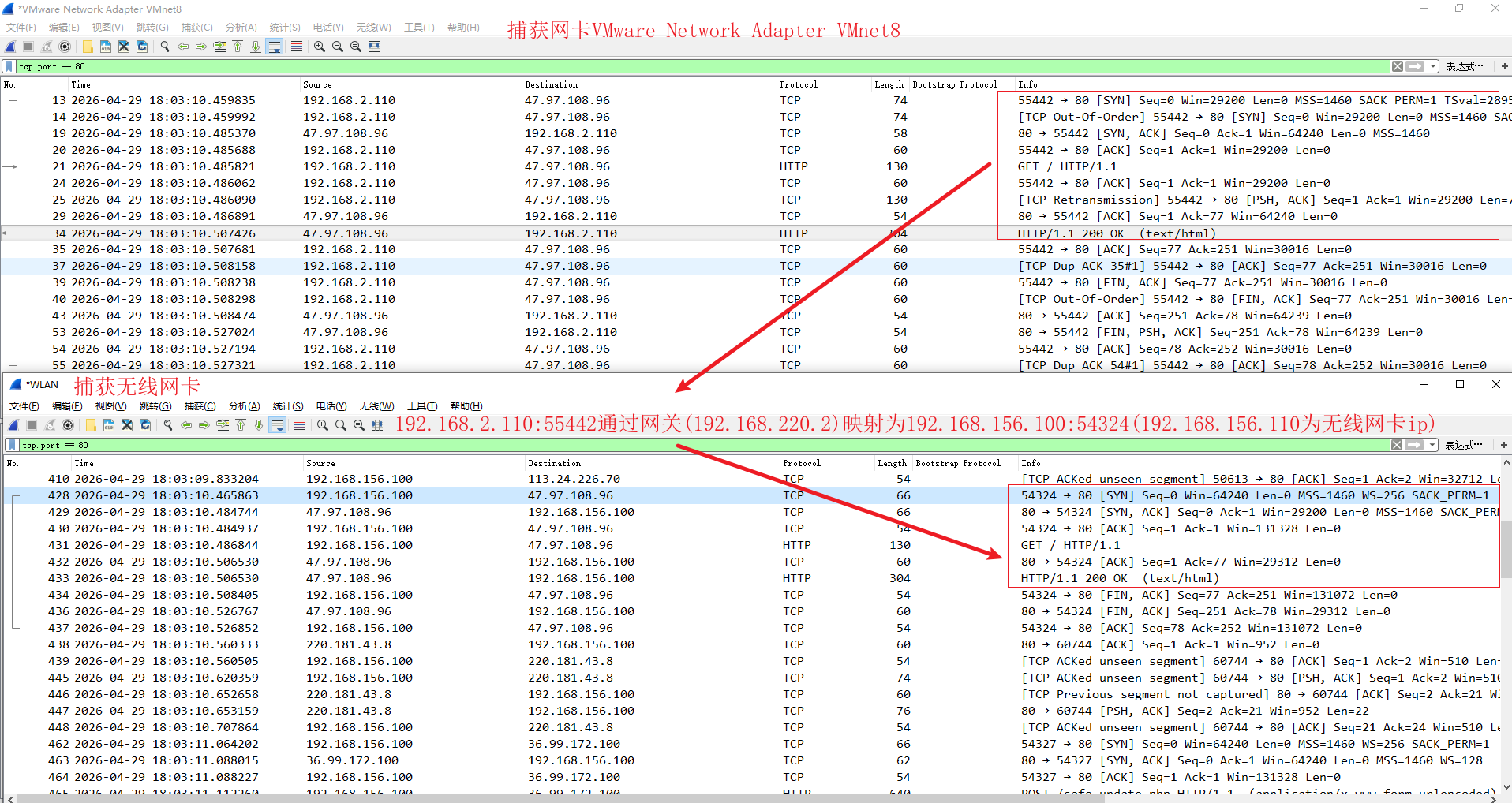
图1
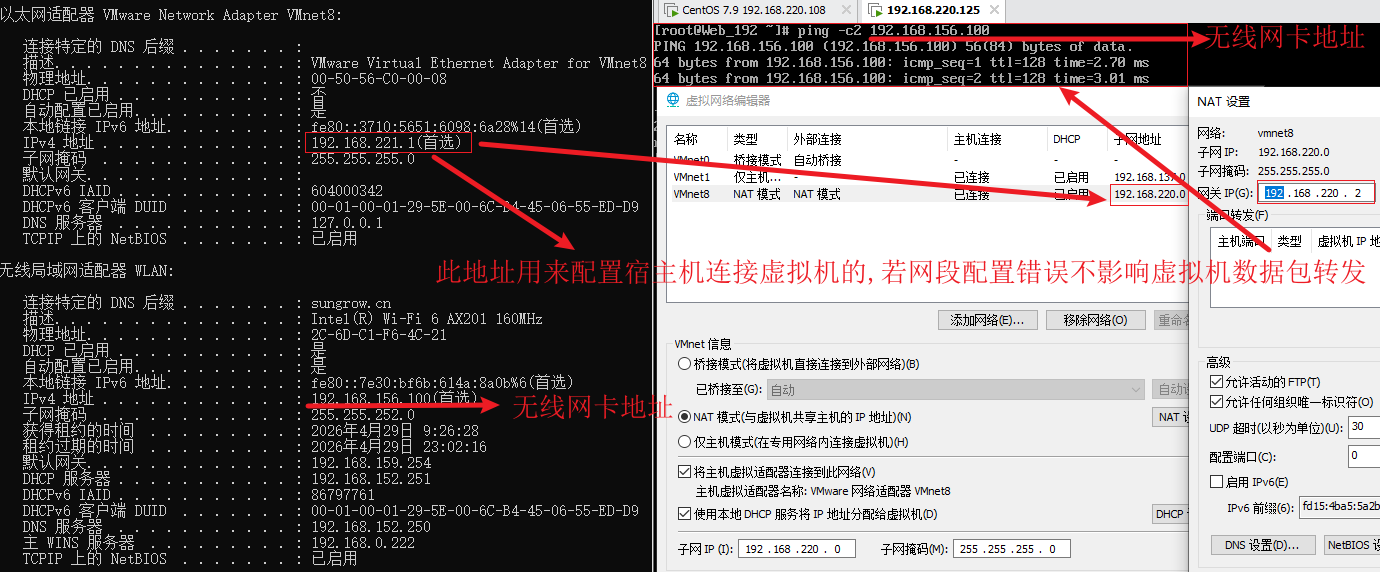
图2
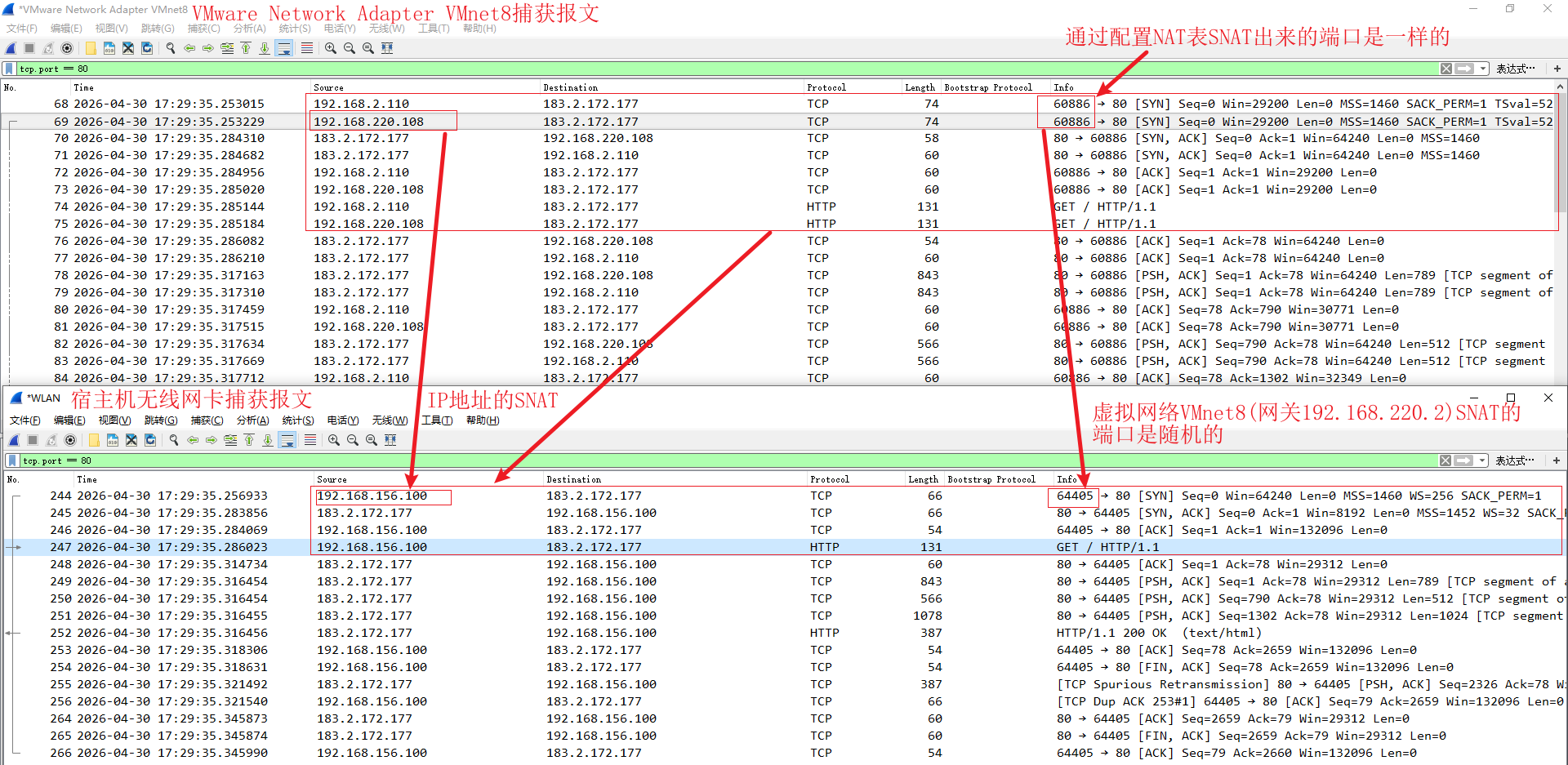
图3
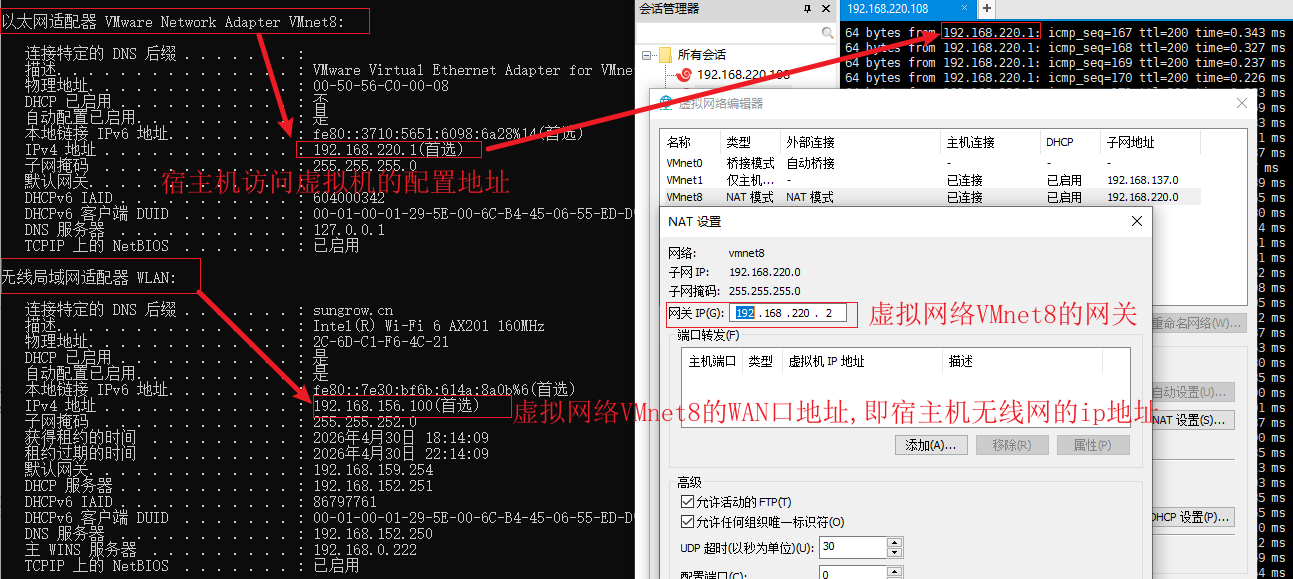
图4

openEuler 是由开放原子开源基金会孵化的全场景开源操作系统项目,面向数字基础设施四大核心场景(服务器、云计算、边缘计算、嵌入式),全面支持 ARM、x86、RISC-V、loongArch、PowerPC、SW-64 等多样性计算架构
更多推荐
 已为社区贡献1条内容
已为社区贡献1条内容







所有评论(0)